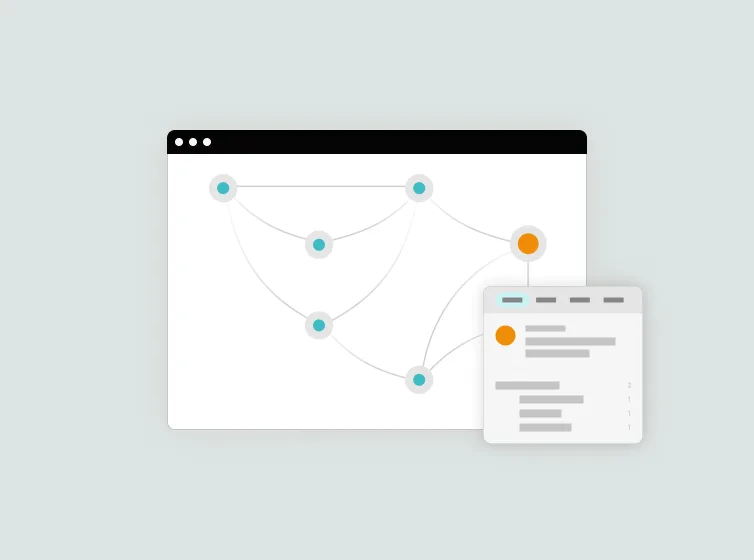
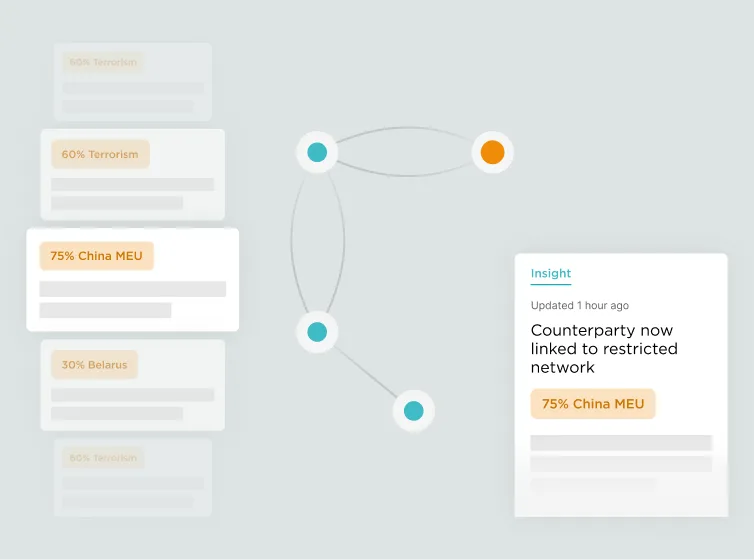
The Bureau of Industry and Security (BIS) Entity List identifies foreign persons — including companies, research institutions, government organizations, and individuals — that are subject to specific license requirements for the export, reexport, or transfer of specified items. For technology companies, the Entity List is one of the most consequential compliance obligations: it restricts the sale of software, hardware, cloud services, AI tools, and other controlled technology to listed entities without a license. The list is updated frequently, with dozens of new additions in a typical cycle, and enforcement actions for violations can include denial orders, substantial civil penalties, and criminal prosecution. Kharon provides expert-verified data on Entity List parties, their affiliates, and their corporate networks — going beyond the published list to identify related parties that may present the same level of risk.