Network Intelligence
Continuous mapping of institutional affiliations, ownership and control structures, and entity relationships where export control risk and foreign state influence can put your research enterprise at risk.

Industry Solutions
Proven at Scale
35+
Leading research universities worldwide
U.S. Treasury
Trusted by
35+
Fortune 100 companies
The Problem
Universities and research institutions are on the front line of a global challenge: preventing the transfer of sensitive technologies and knowledge to foreign military and intelligence programs, state-directed weapons development, and entities that threaten national security. Export controls exist to prevent these transfers — and governments worldwide now expect research institutions to demonstrate compliance well beyond checking names against published restricted party lists. Most export control compliance infrastructure at universities and laboratories was not built for this level of scrutiny.
01
The entities that pose the most complex export control risk to research institutions are increasingly the ones that don’t appear on any published government list. The BIS Entity List names specific entities, but many operate through subsidiaries, affiliated institutions, and front organizations that are deliberately structured to avoid listing. A foreign university’s listed parent may have spun off an unlisted research subsidiary specifically to maintain access to controlled technology. A state-directed laboratory may operate through an intermediary that bears no resemblance to the listed entity. BIS recognized this gap when it adopted the Affiliates Rule in September 2025, extending licensing requirements to entities majority-owned by listed parties. Though the rule is currently suspended through November 9, 2026, the underlying regulatory framework remains in place — and the intelligence gap it was designed to address exists right now, with or without the rule.

02
Research collaborations involve visiting scholars, co-principal investigators, subcontractors, and equipment end-users across jurisdictions. Determining whether a prospective collaborator’s home institution is a military end user (as defined under BIS’s Military End-User Rule, §744.21, or named on the MEU List), an Entity List affiliate, or otherwise restricted requires intelligence that maps institutional networks, and ownership and control structures — not just names on a list. A foreign university may itself be unlisted, yet operate laboratories or subsidiaries that are deeply connected to entities of concern. Individual researchers, too, can carry risk — through undisclosed affiliations with restricted entities, participation in foreign talent recruitment programs, or institutional connections that standard background checks do not reveal. Kharon’s research has shown that Entity List companies have rapidly established new, unlisted subsidiaries specifically to circumvent restrictions. These relationships are deliberately obscured, frequently restructured, and invisible to conventional screening and due diligence.
03
Research at the cutting edge is inherently global — and that global reach puts institutions in the crosshairs of multiple regulatory regimes simultaneously. The U.S. EAR is far from the only framework that matters. Canada layers export controls with research security restrictions under STRAC. The UK expanded strategic export controls post-Brexit. The EU updated dual-use controls in 2025. Australia introduced deemed-export-equivalent provisions for intangible technology supply. Each regime has its own lists, its own licensing requirements, and its own enforcement mechanisms — and a single research collaboration can trigger obligations under several of them at once. A global research enterprise needs intelligence that spans these regimes, not tools built for a single jurisdiction.
The Kharon Approach
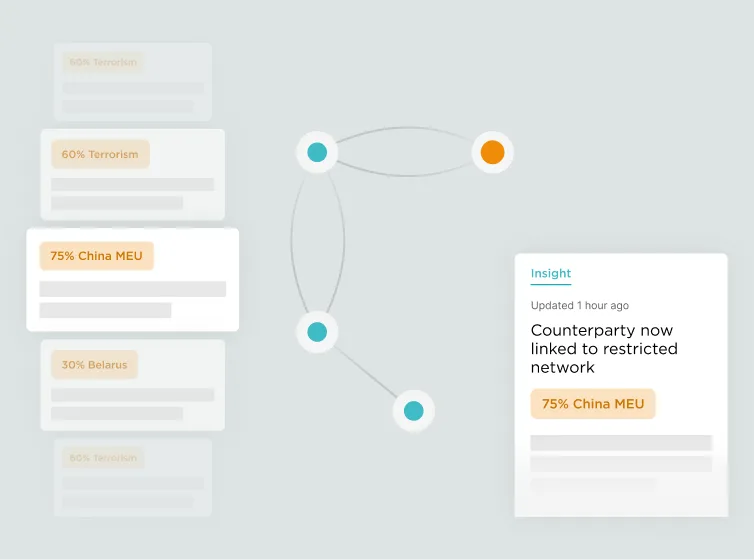
Kharon provides risk intelligence data — underpinned by network analysis and continuous monitoring — that helps research institutions identify, investigate, and manage actual export control risk, not just match names against government-published lists.
All research in the Kharon Core is led and verified by subject matter experts who understand the requirements and challenges of universities and research institutions. Institutional affiliations are validated against source documents. Ownership and control linkages are sourced, documented, and traceable — giving export control and research security officers the defensible, auditable intelligence that federal sponsors and regulators increasingly demand.
Continuous mapping of institutional affiliations, ownership and control structures, and entity relationships where export control risk and foreign state influence can put your research enterprise at risk.
Analyst-led investigations and data sourcing create verified entity data. Affiliations validated. Institutional connections sourced, documented, and traceable.
ClearView, GraphCast, CoreStream, and API as a connected ecosystem — each optimized for seamless integration within your compliance workflow.
Used operationally by the U.S. Department of the Treasury, Department of Homeland Security, Customs and Border Protection, and dozens of other international government partners.
Compliance Workflows
GraphCast delivers curated, continuously maintained datasets that integrate directly into existing screening and research security infrastructure — including Descartes Visual Compliance for restricted party screening and Digital Science’s Dimensions Research Security for research management workflows. Kharon’s data goes beyond published government lists to include Entity List affiliates, military end users, and ownership-linked restricted parties, reducing false positives while surfacing entities that list matching alone misses.
ClearView presents enriched entity profiles, institutional affiliations, and network connections in a single, powerful tool for evaluating prospective research partners, visiting scholars, co-principal investigators, and foreign delegations. Export control officers can trace an individual’s institutional connections through ownership layers and affiliation networks that are invisible to standard screening — determining whether a visiting researcher’s home institution is connected to an Entity List entity, a military end user, or a state-directed research program.
Research institutions operating across borders must navigate a patchwork of export control regimes — U.S. (EAR/BIS), Canada (Controlled Goods Program, SEMA), UK (ECJU Strategic Export Controls), EU (Dual-Use Regulation 2021/821), and Australia (DSGL, Defence Trade Controls Act). Kharon intelligence spans these frameworks, providing a unified risk picture that maps restricted and controlled entities across jurisdictions. In the UK, Kharon’s partnership with HERSA (the Higher Education Research Security Association) supports universities navigating strategic export controls and research security requirements.
As federal agencies implement NSPM-33 disclosure and research security program requirements — with staggered compliance deadlines stretching from 2025 through 2027 — and equivalent policies emerge internationally — including Canada’s STRAC policy (effective May 2024), which bars tri-agency research funding where researchers are affiliated with Named Research Organizations — institutions need tools that identify undisclosed foreign affiliations and connections to restricted or state-linked entities. Kharon’s integration with Digital Science’s Dimensions Research Security platform embeds this intelligence directly into existing research management workflows, mapping affiliations and connections that indicate potential exposure to high-risk entities without requiring researchers or administrators to leave the systems they already use. For institutions seeking a deeper understanding of this challenge, Kharon’s analysis of the university research security challenge explores how leading institutions are balancing collaboration with compliance.
The Kharon Platform
Each tool is optimized for seamless integration within your workflow: from detection, to deep investigation, to operational screening, to automation at scale. Together, our technology allows teams to move fluidly from signal to understanding to action.
Kharon ClearView is a powerful tool for analyzing and visualizing complex entity relationships and associated risk at global scale, supporting the most demanding due diligence, research collaboration vetting, and investigative workflows.

Kharon GraphCast provides curated, continuously maintained datasets aligned to specific risk typologies, including BIS Entity List affiliates, military end users, and export control risk, designed to power complex global screening and monitoring systems for export control, research security, and trade compliance.
The Kharon API enables custom applications and workflows built directly on Kharon insights and risk scores, integrating seamlessly into internal systems to power analysis, automation, and decision-making at scale.
Kharon CoreStream turns fragmented global signals into continuous, personalized streams of insight, establishing a new standard for situational awareness in a complex world.
Solutions by Role
Kharon extends screening coverage past standard restricted party lists, building defensibility into your export control program and daily operations. When BIS, federal sponsors, or institutional leadership ask what intelligence your program relies on, Kharon is a name they recognize and trust.
Proactive identification of undisclosed foreign affiliations, institutional connections to restricted entities, and research integrity risks — with intelligence that helps satisfy certain NSPM-33 requirements and equivalent international research security frameworks. Kharon surfaces the connections that disclosure forms alone cannot reveal.
For Vice Presidents, Vice Provosts, Deans of Research, and other functional leaders: institutional-level visibility into export control and research security risk — whether your institution is a university operating under the Fundamental Research Exclusion, a national laboratory navigating FOCI and facility clearance requirements, or both. Confidence that your compliance infrastructure can withstand federal audit, that research partnerships are vetted with the same rigor government agencies apply, and that your institution’s reputation and future federal funding eligibility are protected in an era of heightened scrutiny.
Simple, clear tools that streamline restricted party checks on grants, contracts, and subawards — aligning compliance with the pace of research administration. Screening decisions documented defensibly, without adding days to the award process.
FAQ
From export control and research security professionals evaluating compliance intelligence solutions.
Under the U.S. Export Administration Regulations (EAR), a deemed export occurs when controlled technology or source code is ‘released’ to a foreign national within the United States. Release includes not just providing documents, but also visual inspection of equipment and facilities, oral briefings, demonstrations, and the application of personal knowledge or technical experience. For universities, this means that a lab tour, a conference presentation involving controlled data, or sharing technical data with a visiting scholar or foreign national employee can each constitute an export — even if nothing physically leaves the country. Institutions must determine whether a deemed export license is required based on the technology’s Export Control Classification Number (ECCN) and the foreign national’s country of citizenship. Similar concepts exist internationally: Australia’s Defence Trade Controls Act amendments (in force since September 2024, with penalties enforceable from March 2025) now make it an offence to supply DSGL technology to a non-exempt foreign person within Australia without a permit — a distinct framework with analogous effect.
The Fundamental Research Exclusion (FRE) under the EAR (§734.8) and ITAR (§120.34) provides that basic and applied research in science and engineering conducted at accredited institutions of higher education is not subject to export control restrictions, provided the research results are ordinarily published and shared broadly. This exclusion is a critical carve-out for universities — but it has important boundaries. The FRE does not apply to research that is subject to access or dissemination restrictions (such as those imposed by federal sponsors), proprietary research, or research conducted under contract with specific deliverables to the government. National laboratories — including DOE national labs, Federally Funded Research and Development Centers (FFRDCs), and University Affiliated Research Centers (UARCs) — operate under additional constraints that most universities do not face. These include facility security clearances, Foreign Ownership, Control, or Influence (FOCI) requirements, and classified program access that can limit the applicability of the FRE. Institutions that span both open academic research and restricted contract work need compliance infrastructure that can distinguish between these categories and apply the appropriate level of screening and control to each.
The Bureau of Industry and Security (BIS) Entity List identifies foreign persons, including universities, research institutes, and companies, that are subject to specific export licensing requirements because they have been determined to pose a significant risk of involvement in activities contrary to the national security or foreign policy interests of the United States. Several major foreign universities and research institutes appear on the Entity List. Institutions must screen potential collaborators, visitors, equipment recipients, and technology transfer partners against the Entity List — and, critically, must also identify unlisted affiliates of these entities. Standard list-matching tools check the published list but cannot map the institutional networks, ownership structures, and subsidiary relationships that connect an ostensibly unlisted entity to a listed one.
National Security Presidential Memorandum 33 (NSPM-33) directs federal research funding agencies to strengthen and standardize disclosure requirements and research security programs at recipient institutions. Institutions receiving more than $50 million per year in federal research funding are required to establish formal research security programs that include cybersecurity, foreign travel security, insider threat awareness, and export control training. Federal agencies are implementing these requirements on staggered timelines: NSF’s disclosure requirements took effect in May 2023, DOE and DOD requirements are in effect, and NIH’s enhanced disclosure and research security program requirements are being phased in through 2026, with USDA and other agencies following through 2027. Compliance requires the ability to identify foreign affiliations and connections to restricted entities across your research enterprise — capabilities that go well beyond standard screening. Comparable requirements are also emerging internationally: Canada’s Policy on Sensitive Technology Research and Affiliations of Concern (STRAC) takes a similar approach, barring federal research funding where any researcher is affiliated with one of 103 Named Research Organizations connected to foreign military or state security entities.
Most approaches to export control compliance at universities rely on matching names against government-published restricted party lists — the Consolidated Screening List, the BIS Entity List, and equivalent lists in other jurisdictions. This catches explicitly named entities but cannot identify their affiliates, subsidiaries, institutional networks, or ownership-linked parties — the exact gap the BIS Affiliates Rule was designed to address. Kharon maps these connections through continuous, analyst-led investigation of ownership structures, institutional affiliations, and entity networks worldwide. The result is intelligence that reveals restricted party risk that list matching alone misses, where all data is readable by AI and LLM-powered systems to ground results in a reliable source of truth. Kharon is complementary to restricted party screening platforms like Descartes Visual Compliance — it provides the intelligence layer that makes existing screening infrastructure more effective.
Yes. Kharon is designed to enhance the systems universities already use, not replace them. GraphCast data files integrate directly into existing restricted party screening software, including Descartes Visual Compliance and other screening platforms common in the university environment. For research security workflows, Kharon’s risk intelligence integrates with Digital Science’s Dimensions Research Security platform, embedding risk intelligence directly into research management systems. The Kharon API enables custom integrations with institutional compliance systems, grant management platforms, and internal workflows.
In September 2025, BIS adopted an interim final rule extending Entity List, Military End-User List, and certain SDN List licensing requirements to any foreign entity owned 50 percent or more — directly or indirectly, individually or in aggregate — by one or more parties on these lists. BIS subsequently suspended the rule for one year through November 9, 2026, but institutions should prepare now for reinstatement: the regulatory trajectory is clear, and organizations that build affiliate identification capabilities ahead of the rule’s effective date will be positioned to comply. For universities, this means that a foreign research institute, laboratory, or company that does not itself appear on any list may still be subject to licensing requirements if it is majority-owned by a listed entity. Identifying these affiliates requires ownership intelligence that standard screening tools do not provide. Kharon’s guide to the BIS Affiliates Rule provides a detailed breakdown of how the rule works and its implications across jurisdictions.
Export control regimes exist in every major research economy, each with distinct requirements. In Canada, the Controlled Goods Program and the Special Economic Measures Act regulate the handling and transfer of controlled goods and technology — and U.S. re-export controls can apply to U.S.-origin technology held by Canadian institutions. Canada’s research security requirements also include the Policy on Sensitive Technology Research and Affiliations of Concern (STRAC), which restricts tri-agency research funding involving researchers affiliated with designated Named Research Organizations. In the UK, the Export Control Joint Unit (ECJU) administers strategic export controls that, since Brexit, extend to transfers to EU partners. The EU’s Dual-Use Regulation (2021/821), updated in September 2025, controls the export, brokering, and transfer of dual-use goods, software, and technology. In Australia, amendments to the Defence Trade Controls Act (in force since September 2024, with penalties enforceable from March 2025) expand controls to include intangible supply of DSGL technology to non-exempt foreign persons within Australia. Kharon’s risk intelligence spans these regimes, providing a unified view of restricted party risk across jurisdictions.
A technology control plan (TCP) is a documented set of procedures that a university or laboratory implements to protect controlled technology from unauthorized access or transfer. TCPs are typically required when an institution handles EAR-controlled technology in settings where foreign nationals may have access — such as shared laboratories, collaborative research projects, or facilities hosting visiting scholars. A TCP specifies who has access, what physical and cybersecurity controls are in place, and how the institution will monitor compliance. Effective TCPs require knowing which entities and individuals pose export control risk — information that goes beyond list matching to include institutional affiliations and network connections.
Effective screening requires more than running a name against the Consolidated Screening List. Institutions should evaluate the prospective collaborator’s institutional affiliations — including whether their home institution, or any parent or subsidiary of that institution, appears on the BIS Entity List, Military End-User List, or equivalent international restricted party lists. They should assess whether the research involves controlled technology under the EAR or ITAR, whether a deemed export license may be required, and whether the collaborator’s institutional network includes connections to military end users or state-directed programs. Kharon provides the network intelligence and institutional mapping that makes this level of diligence practical at the pace research collaboration demands.
Under the Export Control Reform Act (ECRA), criminal penalties for export control violations can reach $1 million per violation and 20 years imprisonment. Administrative penalties can reach $374,474 per violation (as adjusted for inflation; this figure is updated annually) or twice the value of the transaction, whichever is greater. Penalties apply to each individual violation, meaning a single compliance failure involving multiple items or occasions can trigger compounding liability. BIS has signaled that it will treat a decision not to voluntarily self-disclose significant violations as an aggravating factor in penalty calculations. But for research institutions, the financial penalties may be the least of it. Export control violations can trigger institutional debarment from future federal grants, suspension of individual researchers, closure of laboratories, denial of export privileges that effectively cut an institution off from international collaboration, and reputational damage that takes years to repair. Federal sponsors evaluate institutional compliance posture when making award decisions — a documented violation can jeopardize an institution’s ability to compete for funding long after the penalty is paid. Institutions with documented, effective compliance programs may receive significant mitigation — making the quality of the intelligence underlying your program a material factor in both enforcement outcomes and continued funding eligibility.
Leading compliance functions are moving beyond manual screening and reactive workflows toward intelligence-driven, proactive research security programs. AI and data analytics enable institutions to map institutional networks, identify hidden affiliations, and monitor for emerging risk across their research enterprise at a scale that manual processes cannot achieve. Kharon’s platform is built to support this shift — human subject matter experts paired with proprietary technology ensure comprehensive, relevant, verified intelligence, where all data is readable by AI and LLM-powered systems to ground results in a reliable source of truth. As research security requirements expand globally, institutions that invest in intelligence infrastructure now will be best positioned to meet evolving regulatory expectations.
Look beyond basic list matching. The critical capabilities are: (1) affiliate and ownership intelligence — can the tool identify entities connected to restricted parties through ownership, control, or institutional affiliation, not just entities that appear on published lists? (2) Institutional network mapping — can it trace connections between universities, laboratories, subsidiaries, and parent organizations across jurisdictions? (3) Multi-jurisdictional coverage — does it span U.S., Canadian, UK, EU, Australian, and other export control regimes? (4) Integration — does it work with your existing screening and research management systems? (5) Verification — is the data analyst-verified and auditable, or algorithmically generated without human validation? (6) Government trust — is the intelligence used by the agencies that enforce these regulations?
Get Started
Talk to our team about your restricted party screening, research security requirements, and compliance priorities — and see how Kharon’s data and technology can strengthen what you’ve already built.